2016 November Cisco Official New Released 350-018 Dumps in Lead2pass.com!
100% Free Download! 100% Pass Guaranteed!
No doubt that 350-018 exam is a worth challenging task but you should not feel hesitant against the confronting difficulties. Lead2pass is supplying the new version of 350-018 VCE dumps now. Get a complete hold on 350-018 exam syllabus through Lead2pass and boost up your skills. What’s more, the 350-018 dumps are the latest. It would be great helpful to your 350-018 exam.
Following questions and answers are all new published by Cisco Official Exam Center: http://www.lead2pass.com/350-018.html
QUESTION 817
The computer at 10.10.10.4 on your network has been infected by a bontnet that directs traffic to a malware site at 168.65.201.120 Assuming that filtering will be performed on a Cisco ASA.
What command can you use to block all current and future connections from the infected host?
A. ip access-list extended BLOCK_BOT_OUT deny ip any host 10.10.10.4
B. shun 168.65.201.120 10.10.10.4 6000 80
C. ip access-list extended BLOCK_BOT_OUT deny ip host 10.10.10.4 host 168.65.201.120
D. shun 10.10.10.4 68.65.201.120 6000 80
Answer: B
QUESTION 818
Refer to the exhibit. Which effect of this configuration is true? 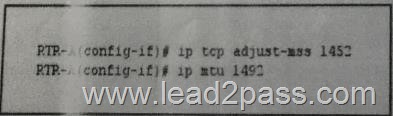
A. The MSS of TCP SYN packets is set to 1452 bytes and the IP MTU of the interface is set to 1942 bytes
B. The maximum size of TCP SYN+ACK packets passing the transient host is set to 1452 bytes and the IP MTU of the interface is set to 1492 bytes
C. The PMTUD values sets itself to 1452 bytes when the interface MTU is set to 1492 bytes
D. SYN packets carries 1452 bytes in the payload when the Ethernet MTU of the interface is to 1492 bytes
E. The maximum size of TCP SYN+ACK packets passing the router is set to 452 bytes and the IP MTU of the interface is set to 1492 bytes
Answer: A
QUESTION 819
Refer to the exhibit. Which effect of this configuration is true? 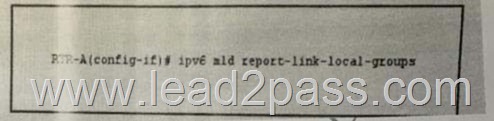
A. It configures the node to generate a link-locak group report when it joins the solicited-node multicast group
B. It enables local group membership for MLDv1 and MLDv2
C. It enables hosts to send MLD report messages for groups in 224.0.0.0/24
D. It enables MLD query messages for all link-local groups
E. It enables the host to send MLD report messages for nonlink local groups
Answer: C
QUESTION 820
You have configured an ASA firewall in multiple context mode. If the context are sharing an Interface.
What are two of the actions you could take to classify packets to the appropriate Context? (Choose two)
A. Enable DHCP
B. Disable MAC auto-generation and adding unique IP addresses to each interface
C. Enable MAC auto-generation globally
D. Assign a unique MAC address to each interface
E. Apply QoS to each interface
Answer: CD
QUESTION 821
Refer to the exhibit. What is the effect of the given configuration? 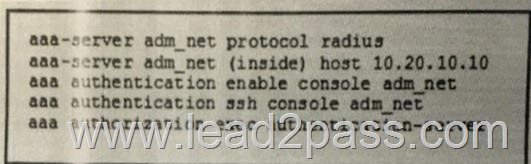
A. It requires the enable password to be authorized by the LOCAL database
B. It allows users to log in with any user name in the LOCAL database
C. It enables management authorization for a user-authenticated RADIUS server
D. Users will be authenticated against the RADIUS servers defined in the adm_net list
E. It allows SSH connections to console login into the ASA
Answer: D
QUESTION 822
What feature enables extended secure access form non-secure physical locations?
A. NEAT
B. 802.1X port-based authentication
C. port security
D. storm-control
E. CBAC
Answer: A
QUESTION 823
What are the two technologies that support AFT?(Choose two)
A. NAT-6to 4
B. NAT-PT
C. DNAT
D. NAT64
E. NAT-PMP
F. SNAT
Answer: BD
QUESTION 824
On an ASA firewall in multiple context mode running version 8.X, what is the default number of VPN site-to-site tunnels per context?
A. 2 sessions
B. 4 sessions
C. 1 session
D. 0 sessions
Answer: A
QUESTION 825
Which three statements about Unicast RPF in strict mode and loose mode are true? (Choose three)
A. Inadvertent packet loss can occur when loose mode is used with asymmetrical routing
B. Interface in strict mode drop traffic witch retun routes that point to the Null 0 interface
C. Strict mode requires a default route to be associated with the uplink network interface
D. Loose mode requires the source address to be present in the routing table
E. Both loose and strict modes are configured globally on the router
F. Strict mode is recommended on interfaces that will receive packets only from the same subnet to which the interface is assigned
Answer: BDF
QUESTION 826
What are the three scanning engines that the cisco IronPort dynamic vectoring and Streaming engine can use to protect against malware? (Choose three)
A. Sophos
B. McAfee
C. Symantec
D. F-Secure
E. Webroot
F. TrendMicro
Answer: ABE
QUESTION 827
Which feature can you implement to protect against SYN-flooding DoS attacks?
A. TCP intercept
B. a null zero route
C. CAR applied to ICMP packets
D. the ip verify unicast reverse-path command
Answer: A
QUESTION 828
What are two advantages of NBAR2 over NBAR? (Choose two)
A. Only NBAR2 allows the administrator to apply individual PDL flies
B. Only NBAR2 supports custom protocols based on HTTP URLS
C. Only NBAR2 supports PDLM to support new protocols
D. Only NBAR2 supports Flexible NetFlow for extracting and exporting fields from the Packet header
E. Only NBAR2 can use Sampled NetFlow to extract pre-defined packet headers for reporting
Answer: BD
QUESTION 829
What are two characteristics of RPL ,used in loT environments? (Choose two)
A. it is distance-vector protocol
B. it is a Interior Gateway Protocol
C. it is link-state protocol
D. it is a hybrid protocol
E. it is an Exterior Gateway Protocol
Answer: AE
QUESTION 830
What protocol does IPv6 Router Advertisement use for its messages?
A. ARP
B. TCP
C. ICMPv6
D. UDP
Answer: C
QUESTION 831
Refer to the exhibit. A signature failed to compile and returned the given error messages.
What is a possible reason for the problem? 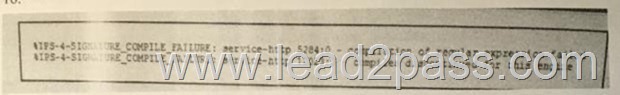
A. Additional signatures must be compiled during the compiling proess
B. The signatures belongs to the IOS IPS Basic category
C. The signatures belongs to the IOS IPS Advanced category
D. There is insufficient memory to compile the signature
E. The signature is retired
Answer: D
QUESTION 832
Refer to the exhibit. What is the effect of the given command sequence? 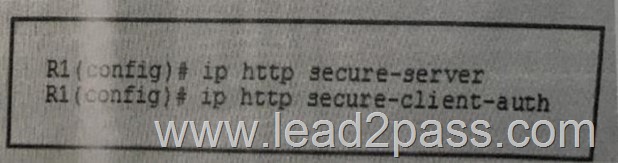
A. The server will accept secure HTTP connections from clients with signed security certicates
B. The client profile will match the authorization profile defined in the AAA server
C. The HTTP server and client will negotiate the cipher suite encryption parameters
D. The clients are added to the cipher suite*s profile
E. The server will accept secure HTTP connections from clients defined in the AAA server
Answer: A
QUESTION 833
Which two network protocols can operate on the application layer? (Choose two)
A. UDP
B. TCP
C. SMB
D. DNS
E. DCCP
F. NetBIOS
Answer: CD
QUESTION 834
When a host initiates a TCP session, what is the numerical range into which the initial sequence number must fall?
A. 1 to 4,294,967,295
B. 0 to 4,294,967,295
C. 1 to 65535
D. 0 to 65535
E. 0 to 1024
F. 1 to 1024
Answer: B
QUESTION 835
Refer to the exhibit. If R1 is connected upstream to R2 and R3 at different ISPs as shown, what action must be taken to preven Unicast Reverse Path Forwarding (uRPF) from dropping asymmetric traffic? 
A. Configure Unicast RPF Strict Mode on R2 and R3 only
B. Configure Unicast RPF loose Mode on R2 and R3 only
C. Configure Unicast RPF Strict Mode on R1 only
D. Configure Unicast RPF loose Mode on R1 only
E. Configure Unicast RPF Strict Mode on R1, R2 and R3
Answer: A
QUESTION 836
What are two features that help to mitigate man-in-the-middle attacks?(Choose two)
A. DHCP snooping
B. dynamic ARP inspection
C. destination MAC ACLS
D. ARP sniffing on specific ports
E. ARP spoofing
Answer: AB
QUESTION 837
Which three statements about the SHA-2 algorithm are true?(Choose three)
A. It generates a 160-bit message digest
B. It generates a 512-bit message digest
C. It is the collective term for the SHA-224, SHA-256, SHA-384, and SHA-512 algorithms
D. It is used for intergrity verification
E. It is provides a fixed-length output using a collision-resistant cryptographic hash
F. It is provides a variable-length output using a collision-resistant cryptographic hash
Answer: CDE
Lead2pass is one of the leading exam preparation material providers. We have a complete range of exams offered by the top vendors. You can download 350-018 dumps in PDF format on Lead2pass.com. Comparing with others’, our 350-018 exam questions are more authoritative and complete. What’s more, the 350-018 dumps are the latest. We ensure you pass the 350-018 exam easily.
350-018 new questions on Google Drive: https://drive.google.com/open?id=0B3Syig5i8gpDU2RpRGdWY3E1NEU
2016 Cisco 350-018 exam dumps (All 894 Q&As) from Lead2pass:
http://www.lead2pass.com/350-018.html [100% Exam Pass Guaranteed]